- Best overall: Splunk
- Best for offline and hybrid environments: VMware Carbon Black Endpoint
- Best for advanced threat hunting: CrowdStrike Falcon Overwatch
- Best for centralized threat management: SolarWinds Security Event Manager
- Best for tandem threat hunting service: ESET Elite
- Best for dedicated SOC support: Trend Micro Managed XDR
- Best for single-command threat mitigation: Heimdal Threat Hunting and Action Center
Cyber threat hunting is a proactive security measure taken to detect and neutralize potential threats on a network before they cause significant damage. To seek out this type of threat, security professionals use cyber threat-hunting tools. These are software solutions driven by advanced analytics, machine learning, and artificial intelligence to detect abnormal patterns in a system’s network and endpoints. They use techniques like behavioral analytics, pattern matching, statistical analysis, and AI/ML modeling.
With reports from Statista indicating that 72% of businesses worldwide were affected by ransomware attacks in 2023, more organizations are looking for cyber threat hunting solutions this year.
In this guide, we explore the top cyber threat-hunting tools for 2024 and compare their features, benefits, and drawbacks.
Featured Partners
Top threat hunting solutions comparison
The table below lists top threat hunting solutions and how their features compare.
| Deployment model | Centralized Log Collection | Automated Threat Detection | Advanced Threat Hunting | 24/7 Monitoring | Pricing | |
|---|---|---|---|---|---|---|
| Splunk | On-premises, Cloud-based, Hybrid | Yes | Yes | Yes | Yes | Contact vendor for a quote. |
| VMware Carbon Black Endpoint | On-premises, Cloud-based, Hybrid | Yes | Yes | Yes | Yes | Contact vendor for a quote. |
| CrowdStrike Falcon Overwatch | On-premises, Cloud-based | Yes | Yes | Yes | Yes | Contact vendor for a quote. |
| ESET Elite | On-premises, Cloud-based | Yes | Yes | Yes | Yes | Contact vendor for a quote. |
| SolarWinds Security Event Manager | On-premises, cloud-based | Yes | Yes | Yes | Yes | Contact vendor for a quote. |
| Trend Micro Managed XDR | Cloud-based | Yes | Yes | Offered as a managed service. | Yes | Contact vendor for a quote. |
| Heimdal Threat Hunting and Action Center | On-premises, Cloud-based, Hybrid | Yes | Yes | Yes | Yes | Contact vendor for a quote. |

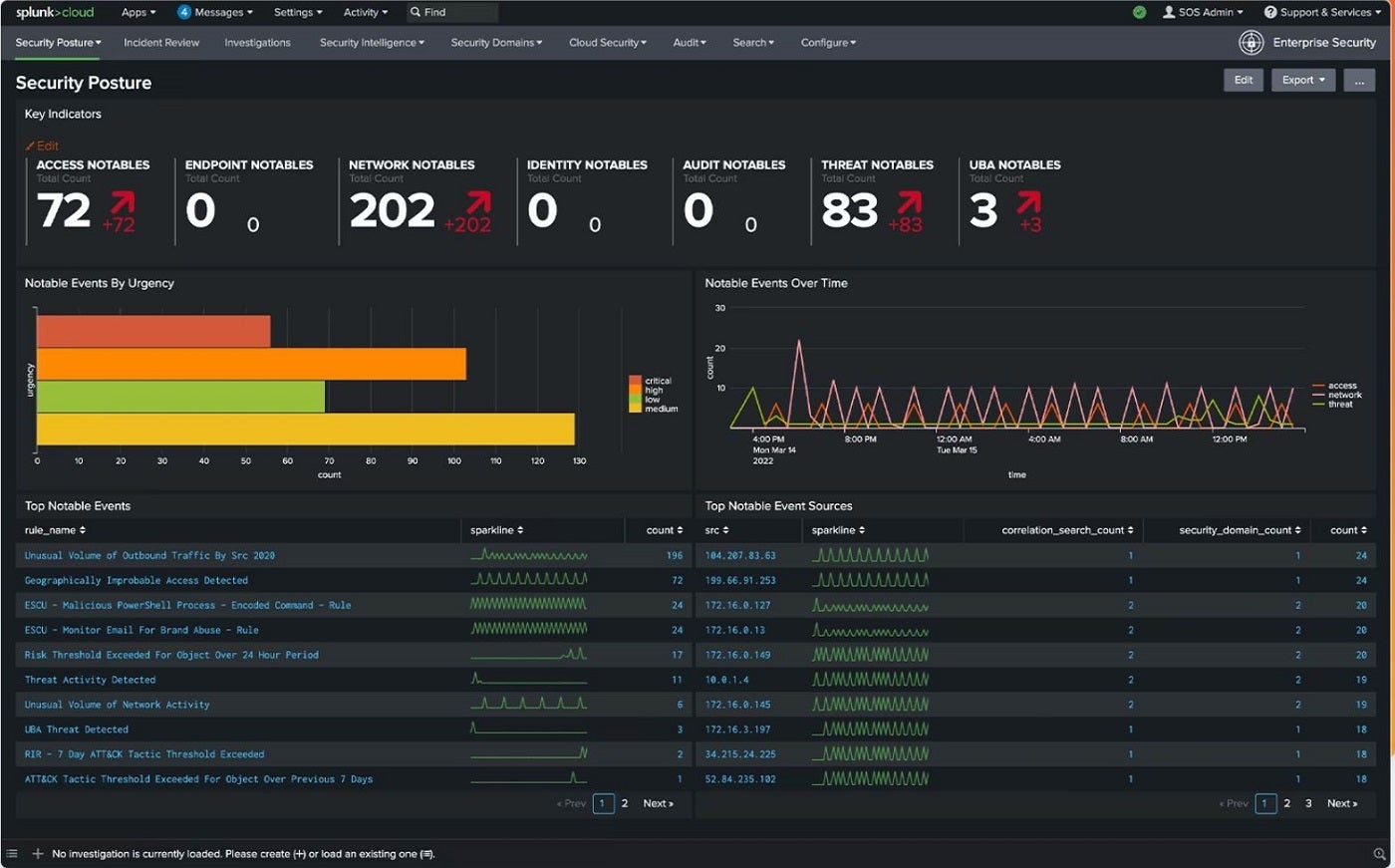
For the best overall cyber threat hunting tool, I recommend Splunk. Offering cloud, on-premises, and hybrid solutions, Splunk as a security information and event management system is top-tier solution to proactively address hidden threats. It brings strong data query functionality that caters to larger security operation functions, such as large-scale threat hunting in enterprises.
SEE: 5 Best Endpoint Detection & Response Solutions for 2024 (TechRepublic)
Through Splunk, security teams can generate threat-hunting queries, analysis routines, and automated defensive rules. A highlight of Splunk’s SIEM capabilities is its speed, being able to detect threats quickly for early stage detection and remediation. It also provides advanced threat detection with about 1,400 detection frameworks and an open, extensible data monitoring platform.
Why I chose Splunk
I chose Splunk for its strong threat hunting capabilities, providing fast detection and analysis no matter the threat. I also have it on the top spot for being well-suited to handle hunting done in large enterprises and organizations. This is especially seen through its diversity in cloud, on-premises, or hybrid threat hunting and extensive detection framework.
Pricing
This solution offers a 14-day trial period. For pricing, contact the vendor.
Features
- Multi-platform integration.
- Open, extensible data monitoring platform.
- Incident review dashboard for quick prioritization of threats.
- Security posture dashboard and threat topology.
- Advanced threat detection.
- Risk-based alerting.
Pros and cons
| Pros | Cons |
|---|---|
| Offers threat intelligence management. | Pricing is ambiguous. |
| Publicly available threat hunting guides. | |
| Customizable event prioritization. | |
| Flexible deployment options. | |
| Rapid and responsive security content updates. | |
| Scalable enterprise-focused threat detection and analysis. |
VMware Carbon Black Endpoint: Best for offline and hybrid environments

If you work in a hybrid or offline environment, I suggest VMware Carbon Black Endpoint, developed by VMware. It’s a threat-hunting tool equipped with behavioral endpoint detection and response (EDR), extended detection and response (XDR), and a next-generation antivirus (NGAV). These features combine with its machine learning capability to deliver advanced threat hunting. The solution continuously records and analyzes endpoint activity and behaviors to detect advanced threats.
SEE: 4 Threat Hunting Techniques to Prevent Bad Actors in 2024 (TechRepublic)
I particularly like how Carbon Black Endpoint can leverage unsupervised machine learning models, being able to detect anomalies that may indicate malicious activity across the cyber kill chain. While its Standard version lacks audit and remediation, I’m confident organizations can gain adequate EDR visibility in offline, hybrid, and disconnected environments.
Why I chose VMware Carbon Black Endpoint
I have VMware Carbon Black Endpoint on this list due to its EDR visibility that covers offline, air-gapped, and disconnected environments.
Pricing
Reach out to the vendor for pricing.
Features
- Next-gen antivirus.
- Behavioral Endpoint Detection and Response (EDR).
- Anomaly detection.
- Increased endpoint and container visibility.
- Automated threat hunting.
Pros and cons
| Pros | Cons |
|---|---|
| Integration with popular security tools like Splunk, LogRhythm, and Proofpoint. | No audit and remediation in the standard version. |
| Supports compliance and audit features. | |
| Endpoint visibility inside and outside of the corporate network. | |
| Advanced Predictive Cloud Security. | |
| Mutual threat exchange between clients. |

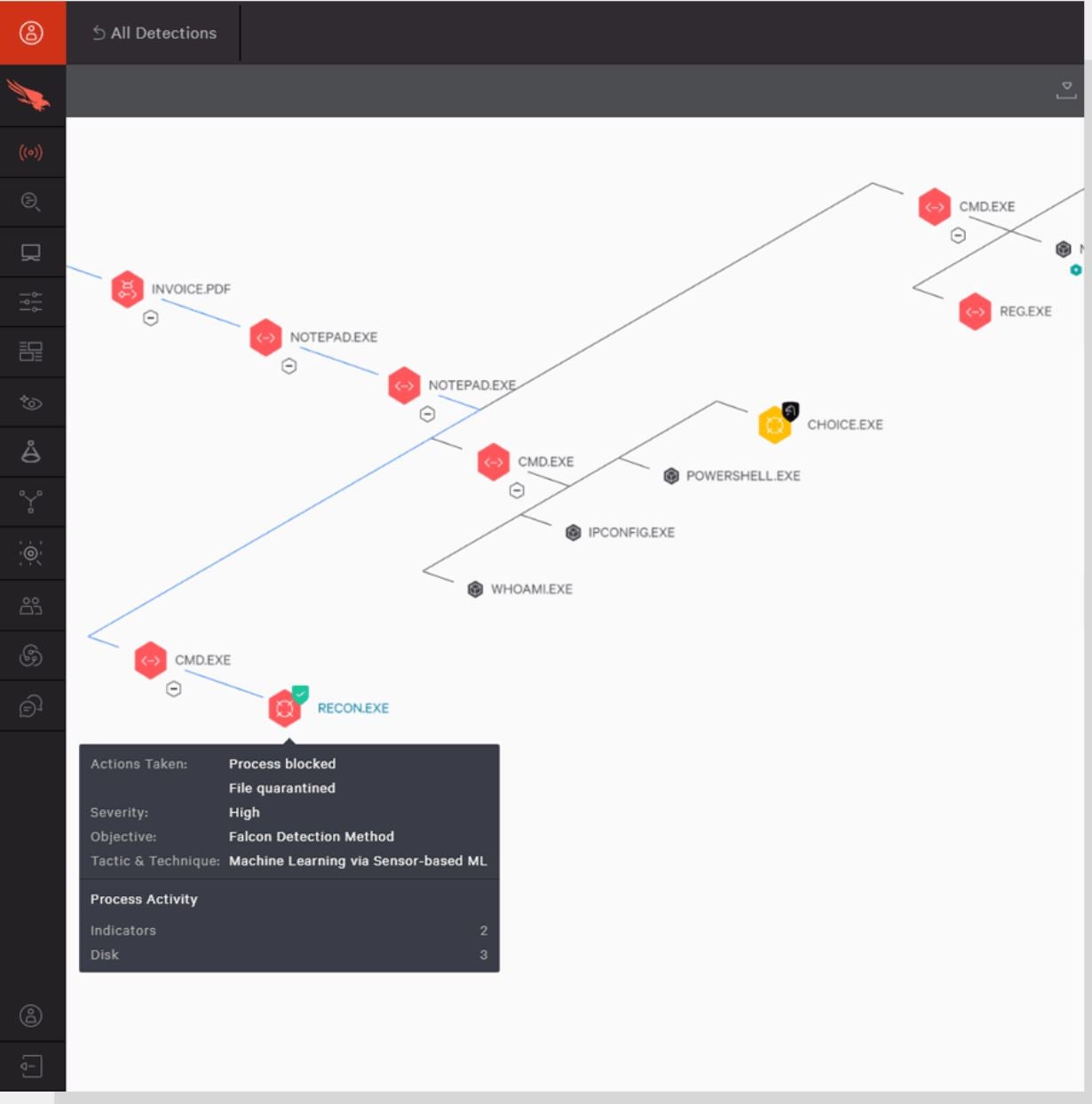
If you plan to conduct advanced threat hunting specifically, I suggest looking at CrowdStrike Falcon Overwatch with advanced EDR and XDR. CrowdStrike’s Overwatch uses its SEARCH methodology to hunt and stop threats. Through this methodology, CrowdStrike’s Overwatch leverages cloud-scale data, insights from in-house analysts, and threat intelligence to mine large amounts of data for signs of intrusion or attack. Also, its lightweight sensor watches and collects data from a vast range of endpoint events uploaded to its cloud storage for analysis.
SEE: CrowdStrike vs Trellix (2024): What Are the Main Differences? (TechRepublic)
An Overwatch feature I find particularly impressive is its threat graph, which helps cyber analysts determine the origins of threats and how they could spread. This can provide useful insight in adopting proactive security measures to prevent any future attacks.
Why I chose CrowdStrike Falcon Overwatch
I picked CrowdStrike Falcon Overwatch for its dedicated approach to advanced threat hunting and automated response to threats, which is achieved by a blend of advanced EDR, XDR, and proprietary features.
Pricing
The CrowdStrike Falcon Overwatch offers a 15-day free trial and features two plans: the Falcon Overwatch and Falcon Overwatch Elite. Contact the vendor for a quote.
SEE: CrowdStrike vs Sophos (2024): Which Solution Is Better for Your Business? (TechRepublic)
Features
- Advanced EDR and XDR.
- Visibility with Falcon USB Device control.
- Automated threat intelligence.
- Threat Graph.
- Firewall management.
Pros and cons
| Pros | Cons |
|---|---|
| Threat alerts are augmented with context. | Threat hunting and investigation coaching are exclusive to Falcon Overwatch Elite users. |
| Includes options for managed service. | |
| Offers a 15-day free trial. | |
| XDR capabilities for advanced threat detection and response. | |
| Quarterly threat hunting reports. |
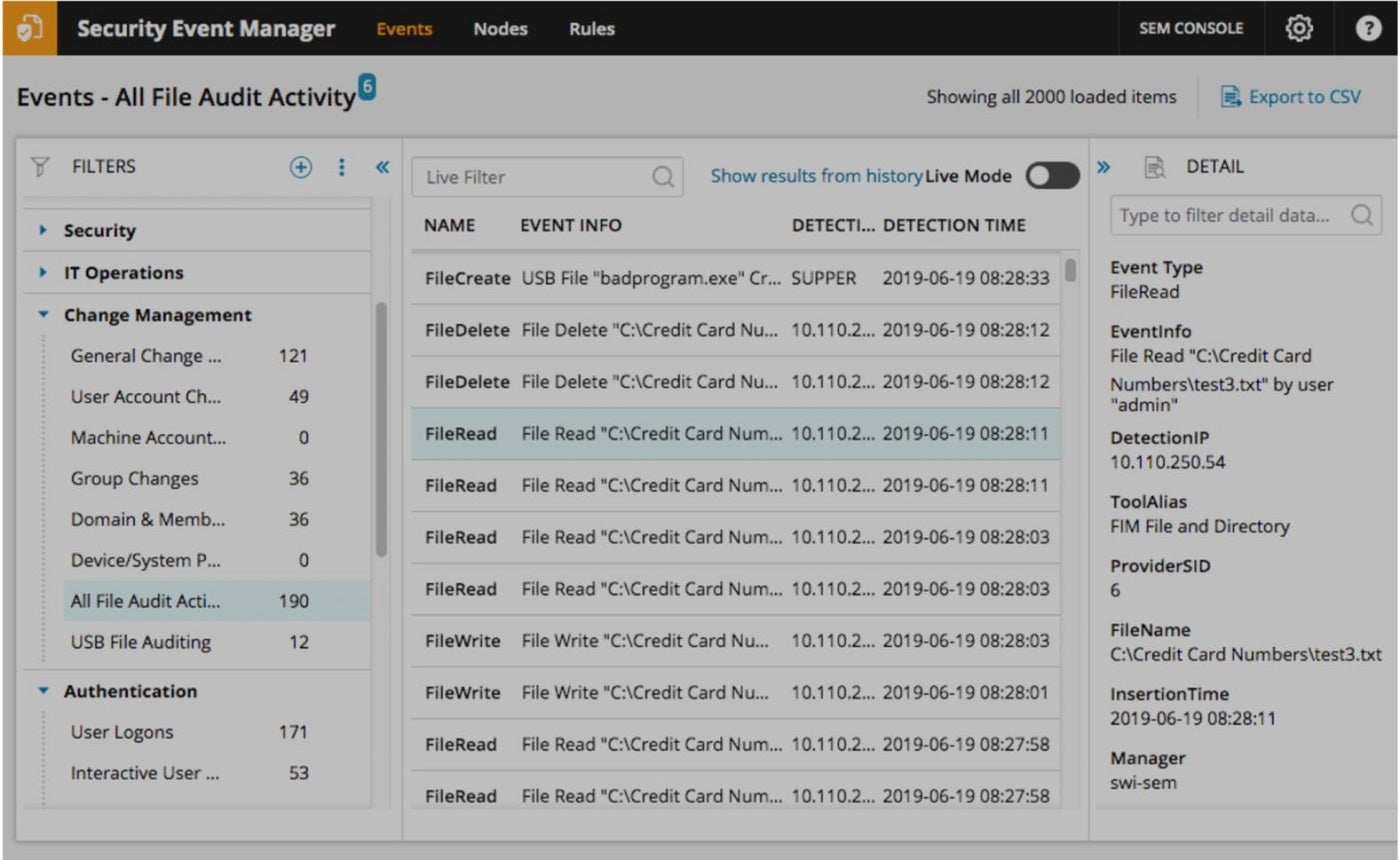
SolarWinds Security Event Manager: Best for centralized threat management

For users looking at centralized threat management, I find SolarWinds Security Event Manager delivers well. SolarWinds provides its threat hunting capabilities through a combination of real-time network performance statistics and data derived from various sources, such as the Simple Network Management Protocol (SNMP) and log entries. The information derived from SNMP allows the system to gather data about network devices, performance metrics, and other critical aspects in real-time.
SEE: Top 8 Advanced Threat Protection Tools and Software for 2024 (TechRepublic)
By parsing and interpreting log data, SEM can identify patterns, anomalies, and potential threats. For me, SEM’s central hub is a noteworthy feature inclusion. It enables security teams to gather, analyze, and respond to security events produced by diverse security technologies, such as firewalls, intrusion detection systems, and endpoint protection solutions.
Why I chose SolarWinds Security Event Manager
I chose SEM due to its centralized platform and seamless integration with various security technologies, offering streamlined security management. This helps security professionals get a bird’s eye view of all possible threats or data that could lead to finding vulnerabilities or possible weaknesses.
Pricing
SolarWinds Event Manager offers subscription and perpetual licensing plans. Contact the vendor for a custom quote.
Features
- Built-in file integrity monitoring.
- Centralized log collection and normalization.
- Integrated compliance reporting tools.
- Advanced pfSense firewall log analyzer.
- Advanced persistent threat (APT) security software.
Pros and cons
| Pros | Cons |
|---|---|
| Offers real-time network performance statistics. | Absence of cloud version. |
| Centralized logon audit events monitor for tracking of security events. | |
| Improved security, real-time monitoring and troubleshooting with advanced pfSense firewall log analyzer. | |
| Integrates with various security technologies for better visibility. | |
| Provides in-depth analysis of log entries to enhance threat detection. |

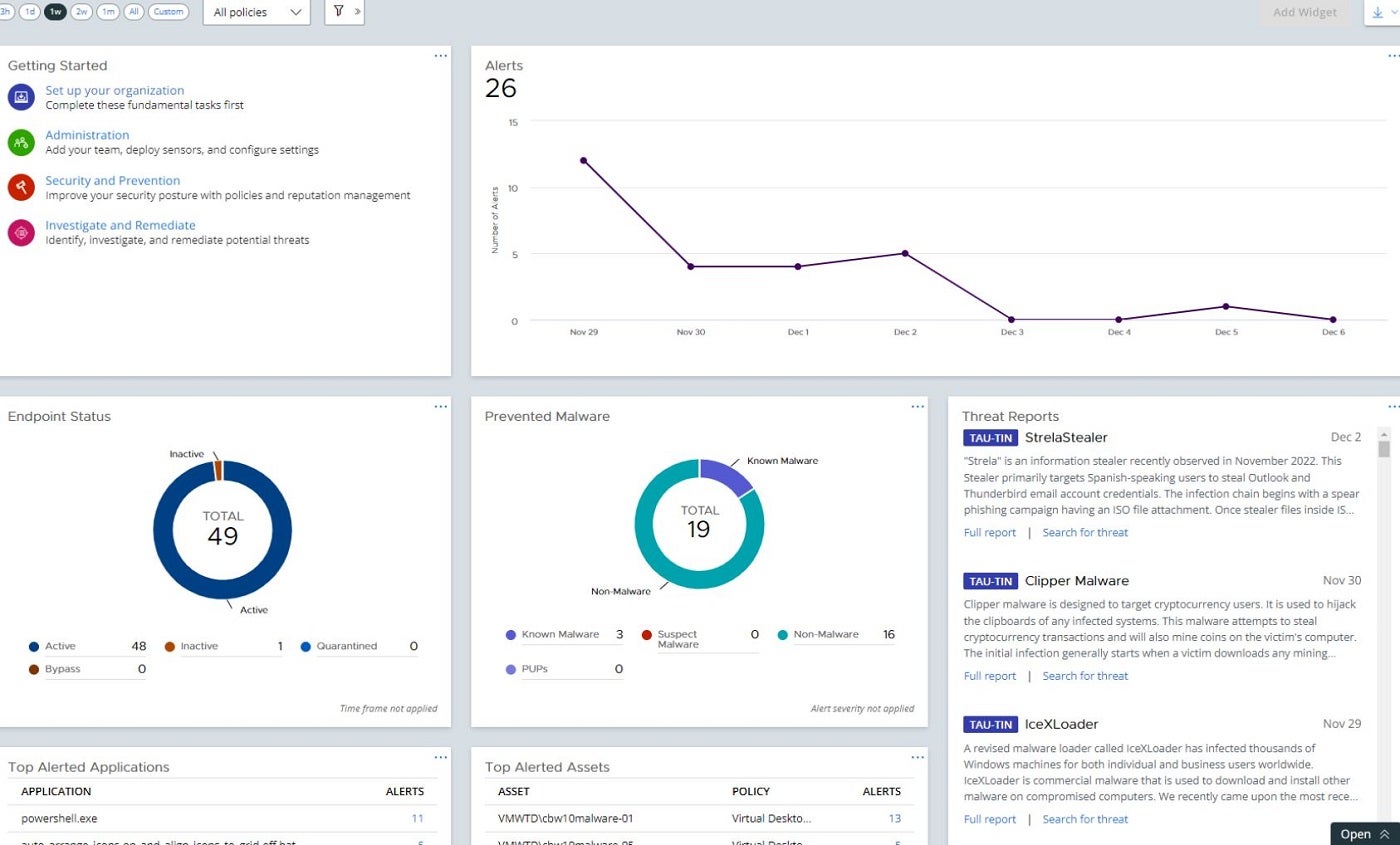
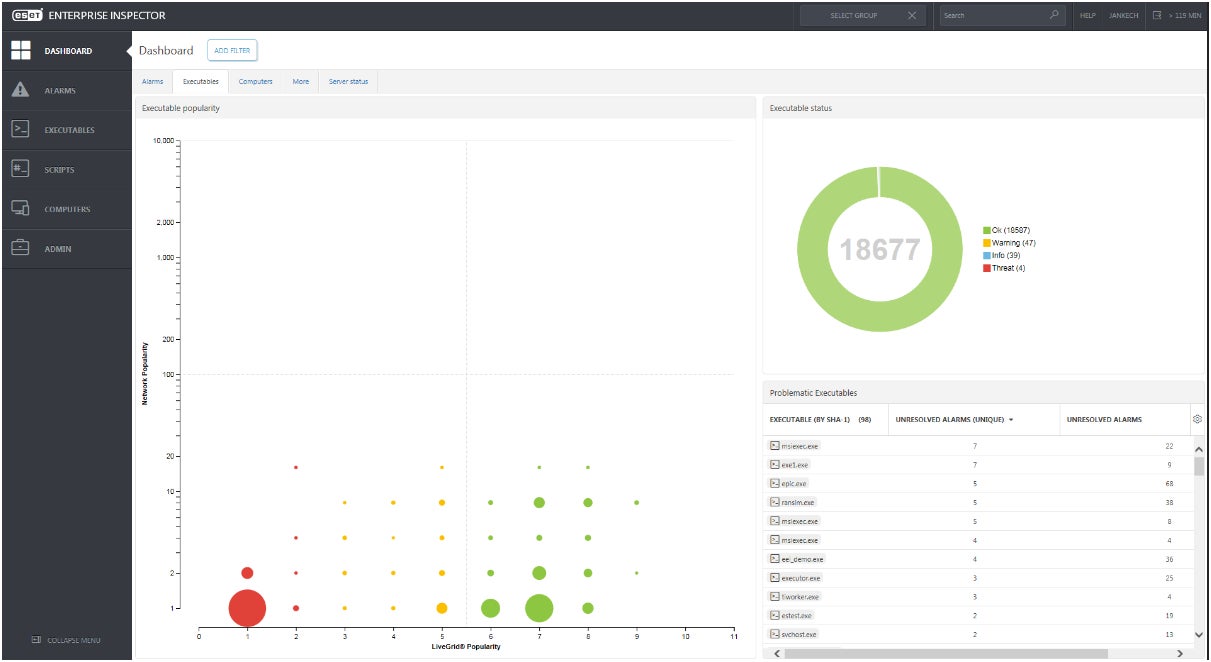
If your company is looking for threat hunting services alongside a dedicated software tool, I suggest ESET Elite. Ths is ESET’s EDR tool that’s built to analyze real time endpoint data and detect persistent threats. Its EDR has the ability to re-scan entire events databases, making it ideal for historic threat hunting. This also helps threat hunters easily find new indicators of compromise by adjusting detection rules as they scan the database.
I especially like how ESET provides their own ESET Threat Hunting service, in tandem with ESET Elite. This is ideal for organizations that don’t have the manpower or dedicated security staff to undergo cyber threat hunting.
Why I chose ESET Elite
I have ESET Elite on this list because it offers a dedicated threat hunting service alongside its ESET Elite EDR. I feel this is a great solution for smaller businesses that don’t have extensive IT or security teams but still want to reap the benefits of advanced cyber threat hunting.
Pricing
It’s best to contact ESET’s Sales team for curated pricing and a proper quotation.
Features
- Behavior and reputation-based detection.
- Automated threat hunting capabilities.
- Can be accompanied with dedicated threat hunting service.
- Protection against file less attacks.
- Customizable alerts.
Pros and cons
| Pros | Cons |
|---|---|
| Easily adjustable detection rules. | May be resource-intensive for older systems. |
| In cloud or on-premises deployment. | |
| Good for businesses with minimal security expertise. | |
| Integrates with other ESET solutions for synchronized response. | |
| Seamless deployment. |

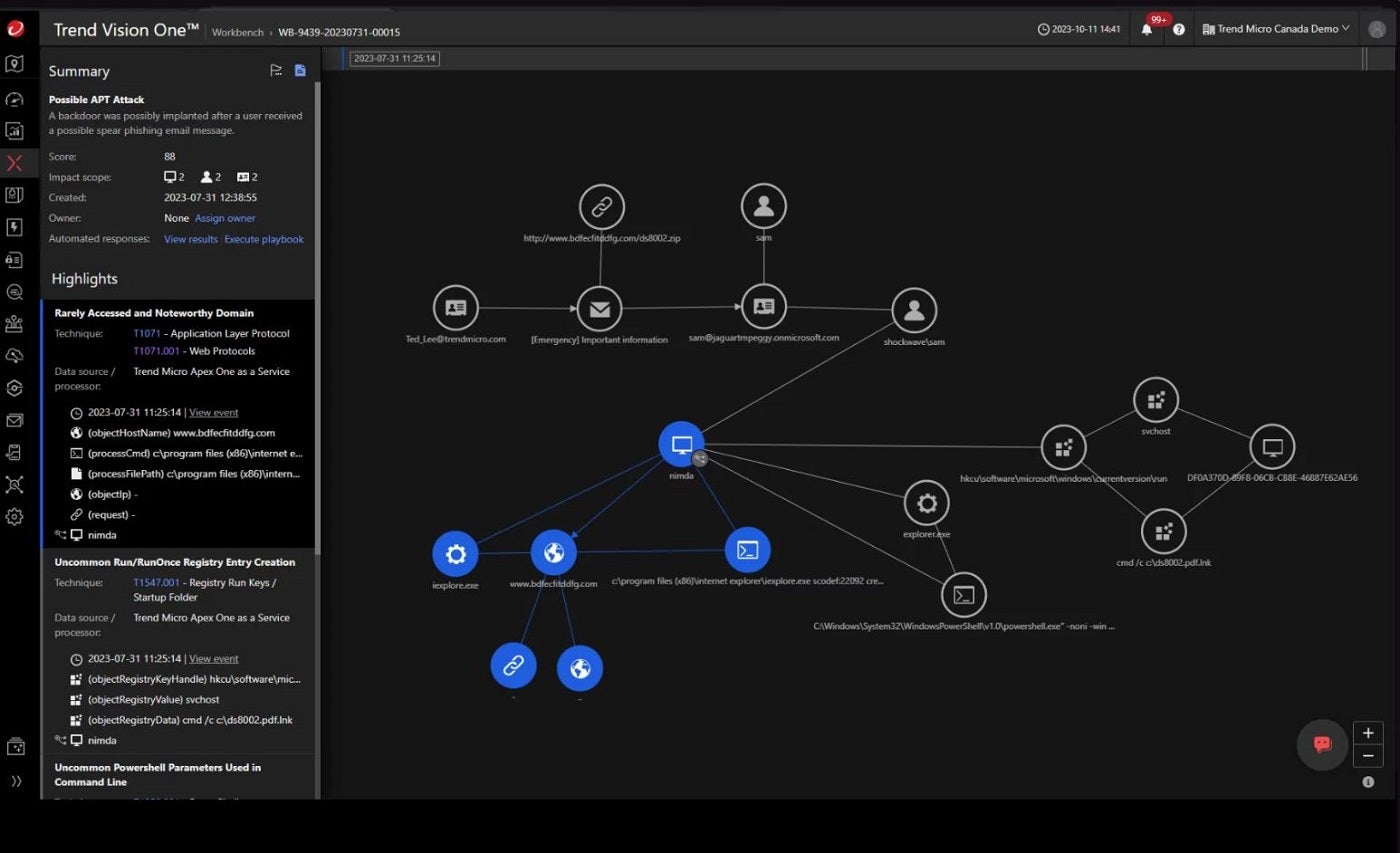
If you need a service with dedicated SOC support, I encourage you to check out Trend Micro Managed XDR. Its security service offers 24/7 monitoring and analysis and stands out for its ability to correlate data from a wide range of sources, including email, endpoint, server, cloud, workload, and network.
I commend Trend Micro for this cross-layered approach, as it enhances threat hunting and provides greater insight into the source and spread of targeted attacks. The solution continuously scans for indicators of compromise or attack, including those shared via US-CERT and third-party disclosures, ensuring a proactive approach to threat hunting.
Another standout to me is how Managed XDR provides dedicated support for Security Operations Center (SOC) teams, reducing the time to identify, investigate, and respond to threats. As part of Trend Service One, it includes premium support and incident response services, extending its value across the product.
Why I chose Trend Micro Managed XDR
I picked Trend Micro Managed XDR for its 24/7 support for Security Operations Center (SOC) teams, and its threat-hunting capabilities that enhance time-to-detect and time-to-respond performance.
Pricing
Trend Micro Managed XDR offers a 30-day free trial. Contact the vendor for pricing.
Features
- Endpoint detection and response.
- 24/7 analysis and monitoring.
- Advanced threat intelligence.
- Cross-layered detection and response.
- Optimized security analytics.
Pros and cons
| Pros | Cons |
|---|---|
| Dedicated support for SOC and IT security teams. | Lack of on-premises solution. |
| Offers server and email protection. | |
| Proactive threat hunting for advanced threats. | |
| Contains threats and automatically generates IoCs to prevent future attacks. | |
| Generates threat alerts and detailed incident reports. |
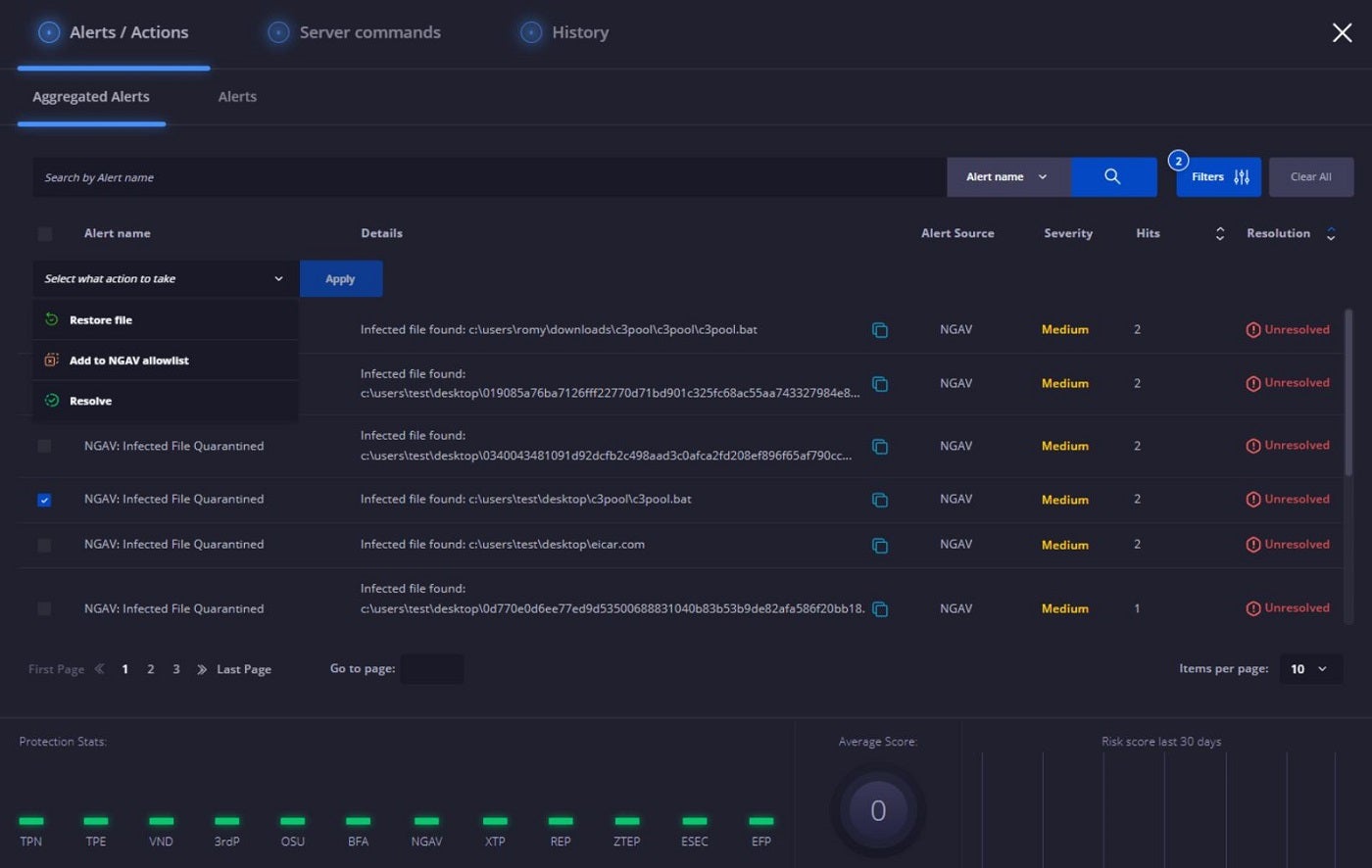
Heimdal Threat Hunting and Action Center: Best for single-command threat mitigation

For convenient, single-command mitigation, I like Heimdal Threat Hunting and Action Center. Heimdal’s threat hunting and detection solution equips SecOps teams and IT administrators with tools for identifying and monitoring anomalous behavior across devices and networks. Leveraging its advanced XTP engine, the Heimdall suite, and the MITRE ATT&CK framework, this platform visualizes relevant information related to endpoints for network-level threat detection.
Users gain insights through risk scores and forensic analysis, which enhances their understanding of potential threats. I personally appreciate the continuous scanning by the XTP engine — adding a strategic layer to threat identification and monitoring. It also allows for prompt remediation with a single command wherever threats are identified.
Why I chose Heimdal Threat Hunting and Action Center
To me, Heimdal stands out because of its one-click execution of commands like scanning, quarantine, and isolation, along with in-depth incident investigation powered by its Action Center.
Pricing
Contact the vendor for a quote.
Features
- Next-gen antivirus, firewall, and mobile device management (MDM).
- Incident investigation and management.
- Activity tracking and monitoring.
- XTP Engine and MITRE ATT&CK framework.
- Quarantine functionality.
Pros and cons
| Pros | Cons |
|---|---|
| Provides a centralized list of the threats detected. | No pricing information available online. |
| Real-time threat monitoring and alerts are provided. | |
| Makes for prompt reporting and statistics. | |
| Single-command remediation is possible with the action center. | |
| Provides a unified view for intelligence, hunting, and response. | |
Key Features of Cyber Threat Hunting Tools
From log analysis and proactive threat identification to intelligence sharing, threat hunting solutions can be equipped with several features that separate them from traditional security monitoring tools. Below are some key features I feel every threat-hunting tool should possess.
Data collection and analysis
Threat hunting tools gather and aggregate vast amounts of data from various sources, such as logs, events, endpoint telemetry, and network traffic. Leveraging advanced analytics and machine learning, unusual patterns and anomalies are determined. These solutions enhance their understanding of potential threats by reviewing or scrutinizing alerts from SIEM systems and Intrusion detection systems (IDS). They analyze the data gathered from firewalls, IDS, DNS, file and user data, antivirus solutions, and other security devices for better insight on what to categorize as potential threats and best remediation channels.
Proactive search and identification of threats
This feature helps security analysts explore and investigate extensive data collected from various sources. The advanced search and query language support enables them to search, filter, and query the data. To do this, security teams can customize and streamline their searches based on certain organizational requirements to extract information like time ranges, specific IP addresses, user accounts, or types of activities. One of the most important aspects of this feature is that not only does it perform real-time analysis by querying live data streams to identify ongoing threats promptly, but it also performs historical data analysis that identifies past incidents or patterns that might have gone unnoticed initially.
SEE: Why Your Business Needs Cybersecurity Awareness Training (TechRepublic Premium)
Collaboration and intelligence sharing
Threat hunting goes beyond individual initiatives, as the data collected and processed individually will be limited. Effective collaboration and intelligence sharing among organizations, security teams, and industry partners are essential, and this can only be achieved by integrating sharable threat intelligence feeds in threat hunting tools. The exchange of threat intelligence, tactics, techniques, and procedures (TTPs) facilitates threat hunting and remediation across diverse organizations.
Behavioral analysis
Threat-hunting tools rely on behavioral analysis to learn and understand normal patterns of user and system behavior. They then utilize techniques such as user and entity behavior analytics (UEBA), machine learning algorithms, and continuous monitoring to identify anomalies, provide context, and enable early threat detection. This feature also helps reduce false positives and enhances proactive identification and response to security risks.
Automated response
This feature prioritizes alerts based on predefined criteria, ensuring that critical or identified threats receive immediate attention. It includes dynamic playbooks, integration with security orchestration platforms, and actions such as incident containment and isolation, user account remediation, and alert prioritization. With automated responses, organizations can reduce dwell time, make incident response more efficient, and achieve compliance with security policies while ensuring that their network and systems are protected against security risks and threats.
How do I choose the best cyber threat-hunting tool for my business?
Choosing the best cyber threat-hunting tool for your individual or business needs borders on many factors, including your personal or business objectives, how the tool fits into your current security infrastructure and your budget. These seven tools are great threat-hunting tools, depending on your personal/business needs.
For example, if you need a dedicated threat hunting service on top of the threat hunting solution, something like ESET Elite is your best bet. On the other hand, if a single action remediation that encompasses scanning, quarantine, and isolation along with an in-depth incident investigation is your goal, then the Heimdal Threat Hunting and Action Center is your best option. The same applies to other tools, as they each have a unique approach to threat hunting and remediation.
However, as with any tool, its effectiveness will depend on how well it is integrated into an organization’s existing infrastructure and security protocols. It’s always recommended to evaluate these tools in the context of your organization’s specific needs and challenges.
Review methodology
For this review, I considered important features of threat-hunting solutions, the diverse approaches each tool uses to detect threats, their remediation processes, integration capabilities with existing systems, and whether the vendors offered personalized support. I gathered information from the different vendors’ websites and review sites like Gartner to gain more insight on each tool. I also considered the developers’ reputations and where they stand in the industry.