- Best for diverse infrastructure: Astra
- Best for pentest automation: Acunetix
- Best for integration with other popular tools: Intruder
- Best for manual pen testing operations: Metasploit
- Best for collaboration: Core Impact
- Best for technical users: Kali Linux
- Best for Unix OS: Wireshark
- Best for detecting SQL injection attacks: SQLMap
Software Spotlight: AstraAstra is a top-tier penetration testing tool that covers a wide range of standards for companies of all sizes.
|
As technology continues to advance, ensuring the security of computer systems, networks and applications becomes increasingly critical. One of the ways in which security professionals can assess the security posture of an entire digital ecosystem is by carrying out penetration testing, or pen testing for short.
SEE: Brute Force and Dictionary Attacks: A Guide for IT Leaders (TechRepublic Premium)
Penetration testing is a fundamental practice for assessing and strengthening the security posture of an organization’s digital assets and is conducted with penetration testing tools. Given the proliferation of these tools, I have come up with a list of the top penetration testing tools available with their features, benefits and drawbacks.
Featured Partners
Penetration testing software comparison table
Here is a feature comparison of our shortlisted pen testing tools and how they stack up against each other.
| Compliance checks | Number of tests covered | Open-source / web-based | Reporting and documentation | Starting price | |
|---|---|---|---|---|---|
| Astra | Yes | 8,000+ | Web | Yes | $1,999 per year, one target |
| Acunetix | No | 7,000+ | Web | Yes | Contact for quote. |
| Intruder | Yes | Not specified | Web | Yes | $157 per month, one application |
| Metasploit | Yes | 1,500+ | Both | No | Contact for quote. |
| Core Impact | Yes | Not specified | Web | Yes | $9,450 per user, user per year. |
| Kali Linux | Yes | Not specified | Open-source | Yes | Completely free |
| Wireshark | No | Not specified | Open-source | Yes | Completely free |
| SQL Map | No | Not specified | Open-source | Yes | Completely free |
Astra: Best for diverse infrastructure

Astra is a penetration testing tool solution with several automated testing features that combine manual with automated penetration testing features for applications, networks, API and blockchains. With over 8,000 tests supported, this tool can help security professionals investigate vulnerabilities within a system. Astra covers different types of penetration testing, including web app pentest, cloud security pentest and mobile app pentest.
SEE: Best Secure Access Service Edge Platforms in 2024 (TechRepublic)
As a comprehensive penetration testing solution, Astra covers many tests that can help organizations meet compliance standards. Some of the compliance standards that Astra can check include SOC2, GDPR and ISO 27001. The Astra tool also integrates with GitLab, Jira and Slack and infuses security into a continuous integration/continuous deployment (CI/CD) pipeline.
Why I picked Astra
I picked Astra for its Enterprise Web App subscription that’s able to accommodate different types of infrastructure. In particular, it can be used on web, mobile, cloud and network infrastructures — offering the ability to have multiple targets across various asset types. This is on top of Astra’s 8,000+ available tests and its wide range of integrations with other popular software.
Pricing
Astra’s pricing is categorized into web app, mobile app and AWS cloud security, each with different pricing.
- Web app: Scanner – $1,999/year, Pentest – $5,999/year and Enterprise – $9,999/year.
- Mobile: Pentest – $2,499/year and Enterprise – $3,999/year.
- AWS cloud security: Under this are the Basic and Elite plans, and both require users to speak to the sales team for a quote.
Features
- Covers 8,000+ tests scanning.
- Covers all tests required for ISO 27001, HIPAA, SOC2 and GDPR.
- Integration with GitLab, GitHub, Slack and Jira.
- PWA/SPAs apps scanning support.
- Support through Slack and Microsoft Teams.

Integrations
- Slack workspaces.
- Jira.
- GitHub.
- GitLab.
- Azure.
- CircleCI.
Pros
- Supports publicly verifiable pentest certificates, which can be shared with users.
- Offers one of the widest testing coverages (over 8,000).
- Tests are automated with AI/ML.
- Support via Slack or Microsoft Teams.
Cons
- What is supposed to be a free trial is charged at $1 per day.
- Support via Slack and MS Teams is only available on the Enterprise plan.
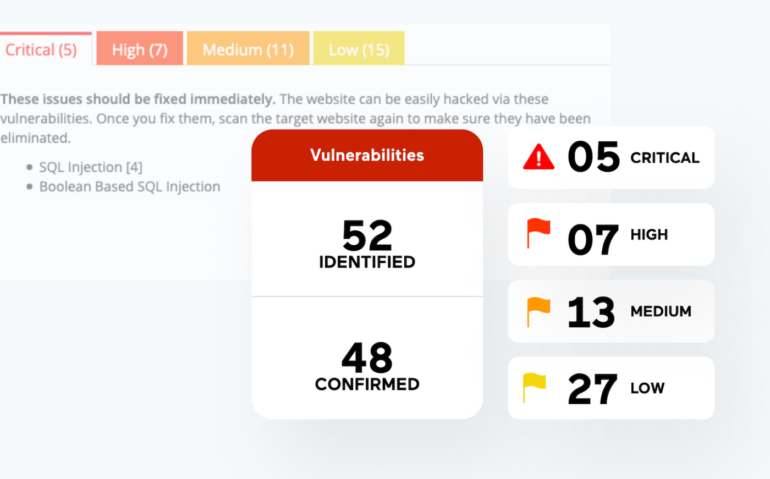
Acunetix: Best for pentest automation

Acunetix by Invicti is a powerful pen testing tool for web applications. The solution is packed with scanning utilities that can help penetration test teams quickly get an insight into over 7,000 web application vulnerabilities and provide a detailed report covering the scope of vulnerability.
Some of the notable vulnerabilities Acunetix can detect include XSS, SQL injections, exposed databases, out-of-band vulnerabilities and misconfigurations.
SEE: Top 8 Advanced Threat Protection Tools and Software for 2024 (TechRepublic)
Acunetix comes with a dashboard that can sort vulnerabilities into classes, such as critical, high, medium and low. The tool is written in C++ and can run on Microsoft Windows, Linux, macOS and the cloud.
Why I picked Acunetix
For businesses specifically looking for automated pentesting, I like Acunetix. It offers scheduled or recurring application scans, includes over 7,000 vulnerability tests and generates useful insights before a scan is half-way through. I imagine it to be a great solution for organizations that want a no-nonsense pentest tool that saves them time, without sacrificing overall security.
Pricing
Contact Acunetix for a quote.
Features
- Vulnerability categorization into an order of severity.
- Over 7,000 web app vulnerabilities are supported.
- Covers the OWASP Top 10 standard for developers and web application security.
- Scan scheduling functionality.
- Compatibility with issue-tracking tools like Jira and GitLab.
Integrations
- Jira.
- Azure DevOps.
- GitHub.
- GitLab.
- Bugzilla.
- Mantis.
Pros
- Detected vulnerabilities are classified according to their severity level.
- Supports reporting and documentation.
- Over 7,000 vulnerability tests are a broad coverage.
- Users can schedule one-time or recurring scans.
- Supports concurrent scanning of multiple environments.
Cons
- No pricing details for users.
- Absence of a free trial.
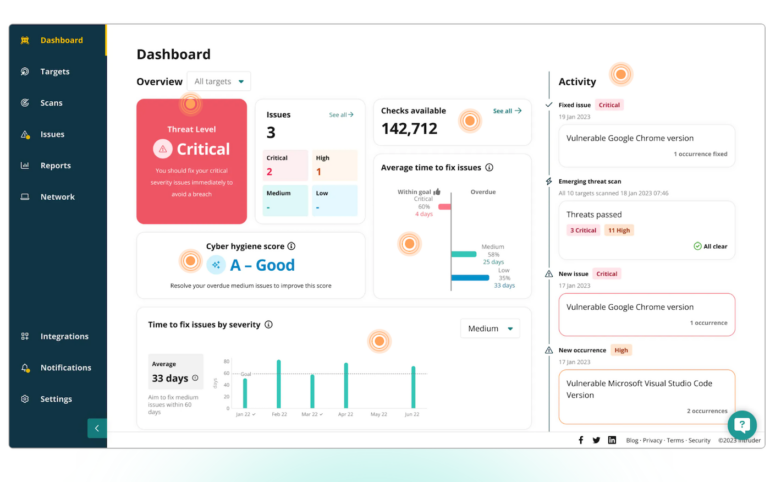
Intruder: Best for integration with other popular tools

Intruder is another handy tool that can help testers discover vulnerabilities in their digital architecture. The software can go beyond vulnerability scans to provide a remediation plan for weaknesses found in the architecture. Intruder services include surface monitoring, continuous vulnerability management, and cloud, web and API vulnerability scanning.
With Intruder, software testers use the thousands of security check options available on the software for pen testing operations. Intruder also comes preloaded with optimization features that automate checking missing patches, misconfiguration issues, cross-site scripting and SQL injection. In addition, it allows integration into team management software like Slack and Jira.
Why I picked Intruder
Intruder carved its name on this list for its strong portfolio of integrations with other work tools and software. In particular, it has established integrations with Slack, Microsoft Teams, GitHub, Azure DevOps, Jira and Zapier, among others.
I also like that it offers a 14-day free trial, allowing interested buyers to test drive the tool without an initial subscription.
Pricing
Pricing is determined by how many applications and infrastructures users want to scan. Here is the pricing detail for one application and infrastructure each.
- Essential: Starts at $157 per month, billed annually.
- Pro: Starts at $221 per month, plus a 14-day free trial.
- Premium: Customized pricing depending on your needs.
Features
- Cloud vulnerability scanning.
- Web vulnerability scanning.
- API vulnerability scanning.
- Compliance and reporting features.
- Internal and external vulnerability scanning.
Integrations
- Amazon Web Services (AWS).
- Drata.
- Jira.
- GitHub.
- GitLab.
- Google Cloud.
Pros
- Offers a 14-day free trial.
- The availability of a demo makes it easier for first-time users to get started with the tool.
- Auto-generates reports for compliance.
Cons
- Does not specify the number of tests covered.
- The 14-day free trial is only available under the Pro plan.
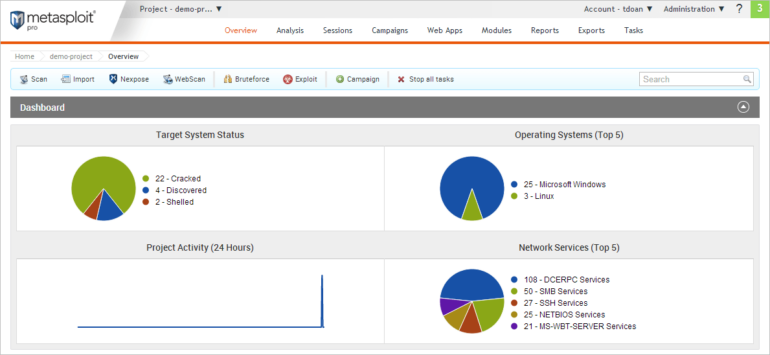
Metasploit: Best for manual pen testing operations

Metasploit is another reliable penetration testing tool for security professionals to consider. The tool can serve users in two major versions — the open-source framework and the commercial support framework. Each version supports both the graphical and command-line user interface. Although the open-source version comes with a lot of features and community support from developers, the commercial version is more robust as it covers more pen testing types.
There are customization features available to optimize the tool according to specific testing needs. In addition, users also have the option of using the tool’s cyberattack mitigation capability and threat simulation environment to help them gain deep visibility into their system.
Why I picked Metasploit
I chose Metasploit for its viability as a prime manual pentest tool. The fact that it offers both an open-source and commercial option provides the customer the choice of what type of pentesting solution they require. This means that businesses will have more latitude in how they pentest their software. Experienced pentesters will appreciate both Metasploit’s polished commercial pentest tool and its open-source developer community, readily available for them to consult with.
Pricing
Metasploit is available in two editions:
- Pro: This edition is suitable for pen testers and security teams and is available for a one-off fee. Contact Metasploit for a quote.
- Framework: This is ideal for developers and researchers and is available for free.
Features
- Integrations via Remote API.
- Automated credentials brute forcing.
- Automated reporting capabilities.
- Task chains for automated custom workflows.
Integrations
- InsightVM.
- Python.
- Core Impact.
- Burp Suite.
- Project Sonar.
- Nexpose.
Pros
- Offers a 30-day free trial.
- Uses a simple web interface.
- Has a free edition for developers and researchers.
- Available as open-source and commercial software.
Cons
- The Framework version is limited in functionality.
- The Github download and setup method might be difficult for new users.
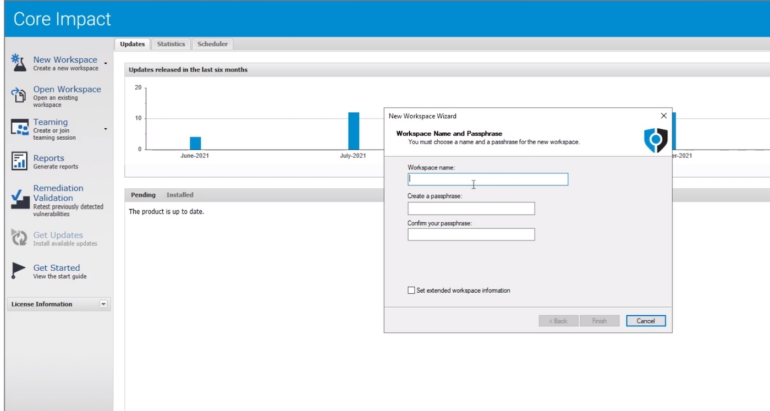
Core Impact: Best for collaboration

Core Impact, now a part of Fortra, ranks as one of the oldest penetration testing tools that have evolved alongside the current demands of a testing environment. The software can facilitate the process of attack replication across endpoints, network infrastructures, web and applications to reveal exploited vulnerabilities and provide suggestions for remediation.
Core Impact reduces the need for manual configuration during installation and testing. Users can easily define test scope and set testing parameters, and Core Impact does the rest. In addition, this tool can generate an attack map, giving users a real-time report of attack activities during testing.
Why I picked Core Impact
I selected Core Impact for its strong focus on team testing. It allows a number of security testers to interact with each in the same session. This allows testing teams to easily share findings and data, as well as smoother delegation of testing tasks. With Core Impact’s emphasis on shared workspaces, testing becomes more efficient and holistic as a result.
Pricing
Core Impact has three pricing plans:
- Basic: Starts at $9,450/user per year.
- Pro: Starts at $12,600/user per year.
- Enterprise: Request a quote.
Features
- Automated Rapid Penetration Tests (RPTs).
- Multi-vector testing capability that includes network, client and web.
- Vulnerability validation of third-party scanner results.
- Centralizes pen testing, from information gathering to reporting.
- Pen testing covers network security, web application, IoT security and cloud security.
Integrations
- Metasploit.
- Cobalt Strike.
- PowerShell.
- Empire.
- PlexTrac.
Pros
- Uses automation wizards to discover, test and report.
- Free trial available.
- Offers broader cybersecurity services.
- New users can learn about the tool via a demo.
Cons
- Pricing is very expensive.
- Free trial does not state how long the trial period lasts.
Kali Linux: Best for technical users

Kali Linux is an open-source pen testing solution that runs on the Debian-based Linux distribution. The tool has advanced multi-platform features that can support testing on mobile, desktop, Docker, subsystems, virtual machines and bare metal.
As an open-source tool, professionals can easily customize it to match their testing situations. There is detailed documentation on using Kali’s metapackages to generate software versions for specific testing purposes. Kali also saves users the time needed to set up tools manually by adding an automated configuration system that optimizes the tool according to different use cases.
Why I picked Kali Linux
Kali Linux is my pick for technical and experienced pentesters looking for a powerful testing solution. It was designed with professional penetration testers in mind, offering a highly customizable architecture that lets pen testers build their own version of the software tailored to their needs.
I particularly appreciate how Kali Linux is upfront in saying that it’s made for veteran pentesters and experienced Linux users, not everyday consumers. This allows their tool to be as good as it can be for their chosen user-base, as opposed to trying to accommodate all users, which may lessen overall quality.
Pricing
It is available completely free of charge.
Features
- Metapackages can be used for specific tasks.
- Offers Live USB Boot for easy booting from a USB device.
- Supports over 600 penetration testing utilities.
- Open-source development model can be accessed on GitHub.
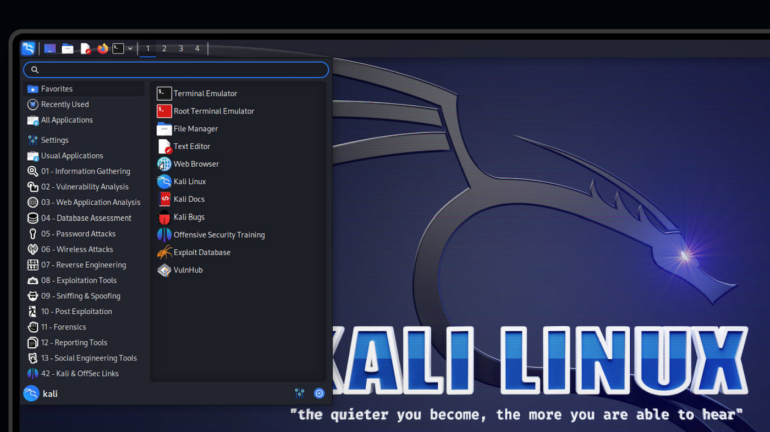
Integrations
- AWS.
- Azure.
- Digital Ocean.
- Linode.
Pros
- Supports a wide array of versions.
- Available for free.
- Courses and documentation are available for new users.
- Multi-language support.
Cons
- Mostly ideal for advanced Linux users.
Wireshark: Best for Unix OS

The Wireshark tool can analyze and test an organization’s network protocol for threats. The tool is a multi-platform penetration testing utility with useful features such as live capture, offline and VoIP analysis.
As an open-source tool, Wireshark provides a lot of support for its users through documentation, webinars and video tutorials. The tool also provides decryption features for arrays of protocols such as Kerberos, SSL/TLS and WEP.
Why I picked Wireshark
I chose Wireshark for being a good pick when it comes to Unix OS users. As a completely free and open source tool, Wireshark allows users to test network protocols and see what’s happening in both broad and fine detail. While it can be technically intimidating, I like the in-depth documentation it provides to users interested in using Wireshark for their specific testing needs.
Pricing
It is available for free.
Features
- Available for UNIX and Windows.
- Capture live packet data from a network interface.
- Display filters for sorting through and analyzing traffic streams.
- Supports offline and VoIP analysis.
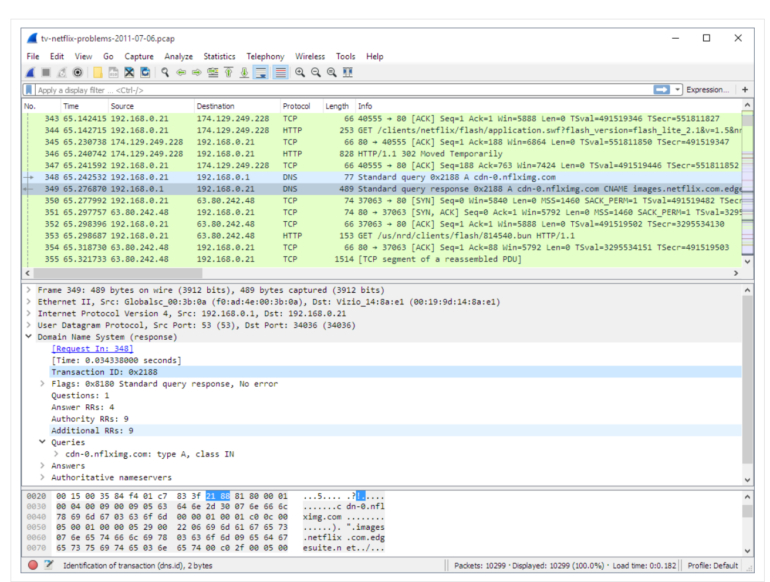
Integrations
- AirPcap.
- YR20 network capture hardware.
- Inside Products.
- C5 SIGMA.
Pros
- It is available for free and is open source.
- There is an export objects function for exporting test results.
- It can be used for decryption across a wide range of protocols.
- Quality documentation for new users.
Cons
- Setup might be too technical for new users.
- Limited automated functionalities.
SQLMap: Best for detecting SQL injection attacks

For open-source lovers, SQLMap is an excellent penetration testing tool for detecting and exploiting SQL injections in applications. Penetration testers utilize the tool to hack databases and understand the depth of vulnerabilities.
In addition, SQLMap has a testing engine that can run several SQL injection attacks simultaneously, reducing the time spent running the test. Some notable servers supported on the platform are Microsoft Access, IBM DB2, SQLite and MySQL.
It is also a cross-platform tool, supporting macOS, Linux and Windows operating systems.
Why I picked SQLMap
For businesses looking to protect against SQL injection attacks, I strongly recommend having SQLMap on your list. It’s a high quality pentest tool that’s designed to detect SQL injections automatically in all types of applications. It covers a wide range of injection attacks and techniques and has extensive support for numerous database management systems. SQLMap is free and has a good amount of documentation available online.
Pricing
Available for free.
Features
- Supports multiple SQL injection techniques.
- Automatic recognition of password hash formats.
- Support for cracking passwords using a dictionary-based attack.
- Can execute arbitrary commands and retrieve their standard output.
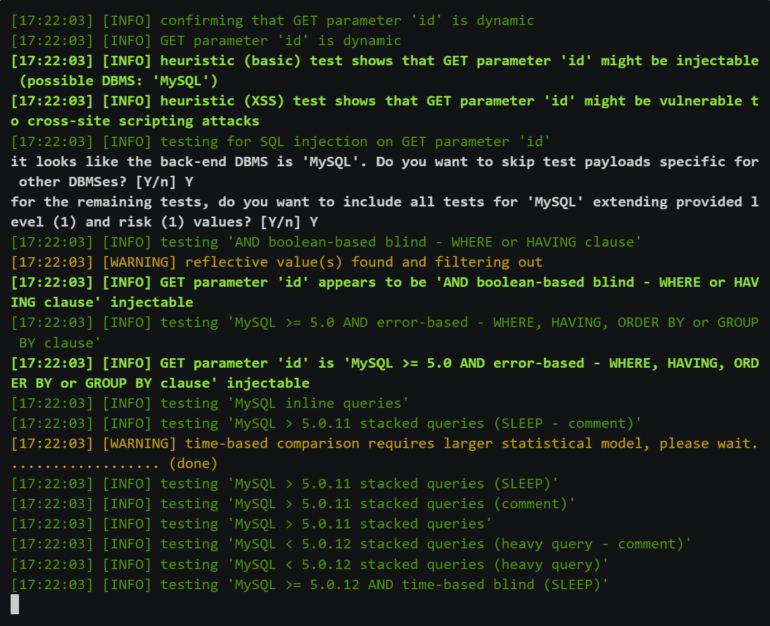
Integrations
- Burp Suite.
- Metasploit.
- Nmap.
Pros
- Covers a broad range of SQL injection techniques.
- Compatible with multiple database management systems like MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2 and more.
- Available for free.
- Has good documentation.
Cons
- Only suitable for command-line users.
Penetration testing solutions offer several features and use cases depending on the objective of the user. Below are the key features of penetration testing solutions.
Vulnerability scanning
Penetration testing often involves vulnerability scans that search for weaknesses and loopholes in software applications, networks and systems. These scans can detect potential vulnerabilities, such as outdated software versions, misconfigurations and known security flaws.
Network mapping and reconnaissance
Network mapping and reconnaissance refer to the process of gathering information and creating a visual representation of a network’s infrastructure and its connected devices. Before launching an attack, hackers typically gather information about their target. Similarly, penetration testing tools assist with reconnaissance activities by mapping networks, identifying active hosts and collecting information about the target infrastructure. This feature aids security professionals in understanding the organization’s digital footprint and potential entry points for attackers.
Traffic analysis and sniffing
Some penetration testing tools can analyze network traffic and capture packets. This capability allows security professionals to monitor and inspect network communication, identify potential vulnerabilities and detect any suspicious or malicious activities. By analyzing network traffic, organizations can gain valuable insights into the security posture of their systems.
Reporting and documentation
Effective communication of vulnerabilities and recommended mitigation strategies is essential in the penetration testing process. Penetration testing tools offer reporting and documentation features to generate comprehensive reports detailing identified vulnerabilities, steps taken during testing and recommendations for remediation. These reports aid in the prioritization and implementation of security measures and compliance verification processes.
Customization features
Different organizations have unique security requirements. These tools often offer customization options and extensibility features, allowing security professionals to tailor the testing process to their specific needs. Customization empowers organizations to focus on their most critical assets and assess vulnerabilities that are specific to their environment.
How do I choose the best penetration testing software for my business?
Given the avalanche of pen testing tools available to security professionals, choosing the right pen testing software is often a challenge. Here are key considerations to help you choose the best penetration testing software for your specific business needs.
Identify your pen testing goals
Before getting started with the selection process, clearly define your objectives for conducting penetration testing. Determine what you aim to achieve through the testing process, such as identifying vulnerabilities in your systems, assessing the effectiveness of your security controls, or meeting regulatory compliance requirements. Understanding your goals will help you narrow down the software options that align with your specific requirements. As can be seen from our comparison table, some of the tools are better than others for different scenarios.
Consider testing methodologies
Penetration testing can be conducted using different methodologies, such as black box, white box, or gray box testing. Evaluate the software’s capability to support the desired testing methodology. Some tools may specialize in specific types of testing, so be sure to check that the software aligns with your preferred approach. Flexibility in supporting various testing methodologies can be beneficial if you require different approaches for different systems or scenarios.
Consider ease of use and user interface
You should consider the user-friendliness of the software and the intuitiveness of its user interface. Penetration testing involves complex processes, so it’s important to choose a tool that is easy to navigate and understand. A well-designed user interface and clear documentation can significantly enhance your experience with the software and improve productivity. While some of the penetration testing tools I shortlisted offer both GUI and command-line interfaces, some only support the command-line interface. Although both interfaces lead to the same result, advanced users may be more comfortable with the command-line interface than average users.
Consider compatibility and integration options
Assess the compatibility of the software with your existing IT infrastructure. Ensure that the tool can seamlessly integrate with your systems, networks, and applications without causing disruptions. Compatibility considerations include the operating systems, databases, and programming languages supported by the software. Additionally, verify whether the tool can integrate with other security solutions you currently use, such as vulnerability management platforms or security information and event management systems.
Check for security and compliance
Given the sensitive nature of penetration testing ensure that the software itself adheres to industry best practices. Assess the software’s ability to handle confidential information securely and maintain the privacy of your testing activities. Additionally, consider whether the tool supports compliance requirements specific to your industry or location.
Best practices for penetration testing
Definition of scope and budget
Sometimes you think it’s ideal to test your entire system environment; however, defining the cost of testing your entire software ecosystem may convince you otherwise. Every organization has high and low vulnerability points. High-risk points are the areas that malicious actors can easily exploit. They can include application code base, configuration files and operating systems. Knowing the scope of the test beforehand is an excellent way to help the organization plan a penetration testing budget.
Financial and customer data should be included
Many organizations handle high volumes of financial and customer records in their database. This set of data is crucial to any organization and must be protected at all costs against breaches. There should be comprehensive penetration testing on these data resources and the software tools that often connect to them.
Consider testing remotely accessible resources
Your organization’s penetration testing plans should not exclude your remote resources and employees. Organizations that support remote roles sometimes provide remote access to valuable resources, which can be an entry point for hackers due to poor security monitoring. Remote resources with limited security monitoring systems should be covered in the penetration testing.
Methodology
To curate our list of the best penetration testing tools, I conducted extensive research by extracting information from official websites, product documentation, case studies, and user feedback from reliable third-party review sites. The criteria that informed our choice include the key features and functionalities covered by the pen testing solution, the community around the software, the user base/popularity of the software, ease of use and the quality of documentation offered by the software. All these factors informed our selection process for this review.




